Your network is not as secure as you think, especially in the eyes of cyber attackers. It’s common knowledge that anyone can be vulnerable to cyberattacks, and it’s up to you to put up strong defenses against attacks when they arise.
The sole decision to secure your network with penetration testing could be your saving grace against a malicious attack.
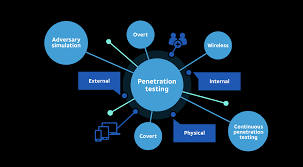
Read along as we discuss the benefits of penetration testing and how penetration testing works.
What is Automated Penetration Testing?
Automated penetration testing is the process of using advanced testing tools to evaluate the security architecture of a system. You get the most out of automated penetration testing by implementing it regularly to stop cyber threats and attacks in their tracks.
Automated penetration testing is an advanced form of manual penetration testing. It uncovers vulnerabilities faster, leveraging machine learning and algorithms to find flaws in systems.
What are the benefits of automated penetration testing?
Assessing vulnerabilities in your network or web applications with automated penetration testing helps you stay ahead of cybercriminals.
Once you detect vulnerabilities, you block them to prevent intrusions. It is a highly recommended proactive cyber security measure to secure your system ahead of time.
Due to its effectiveness, automated penetration has become a common technique against cyberattacks. Let’s look at some of its benefits.
1. Identify the risks
Automated penetration tests help you identify many, if not all, of the security risks within your network. At the end of the test, you have an overview of all risks, from most dangerous to least dangerous.
This assessment is the foundation of your testing as it gives you an overview of vulnerabilities within your network through a vulnerability scanning method. You can launch defense strategies by prioritizing the most urgent needs.
2. Assess the ability to prevent cyber attacks
Automated penetration testing helps you measure how well you and your team can respond to cyber attacks. A thorough assessment in this regard exposes your cyber security weaknesses as strengths.
The evaluation results show you where you need to improve and where you need to praise yourself for a good job done so far.
3. Build Trust
Security breaches are dangerous for organizations as they can lead to exposure of private data. With automated penetration testing, you can assure your customers that their data is secure.
Keeping customer data secure goes a long way in maintaining your company’s image and reputation. People will be more comfortable doing business with you.
4. Prevent network downtime
Network downtime affects workflow and causes financial loss. Penetration testing helps keep your system in good shape, fixing problems that can cause network downtime.
As with most proactive cyber security measures, automated penetration testing is most beneficial when you do it regularly. You get a chance to root out cyber threats before they take root.
How does automated penetration testing work?
Automated penetration testing is ideal for ensuring the security of your network or applications. When done correctly, the automated penetration testing process probes all devices and ports in the network systems of the target environment using selected penetration testing tools.
But how exactly does automated penetration testing work? let’s find out.
1. Planning Phase
The planning phase involves identifying the systems you want to test and the best way to execute the tests. The goal here is to identify the flaws in your network.
To make a solid diagnosis, you need to define the scope and goals of the intended test. The general idea behind this step is to help you gather the intelligence you need within your network, domain names, and possibly mail servers. This is necessary in order to detect possible vulnerabilities in your system.
2. Scanning and Reconnaissance Phase
At this stage, you need to fully understand how your network applications will respond to various intrusion attempts. Static code analysis or dynamic code analysis is a good place to start.
Static code analysis is a method of debugging by examining the source code of a network before running the program. This will help predict how your network will behave when the scan starts. Using static analysis tools, you can scan the entirety of an application’s code in a single pass.
Dynamic analysis is the process of examining the source code of a running program. Here, you analyze your computer software using real or virtual processors.
With the dynamic analysis method, you can monitor the performance of an app in real-time, which is more useful.
Compared to static analysis, dynamic analysis is a more practical way of scanning your system.